Although nothing is ever 100% secure, you can avoid threats with minimal effort.
And it’s great to know that windows Server is just as securable as any Linux box.
But knowing what to do to secure your Windows server isn’t always clear. Hopefully this blog post will give a bit of inspiration for quick security wins you can make on your Windows server.
10 Easy Ways to Secure your Windows Server
Here’s a quick overview listing some easy ways to lock down Windows Server security, and keep the hackers and malware away.
1. Install only required OS components
By default, Windows wants to install the full version of the OS. But instead, go for a minimal custom install.
Non-required components should be left out.
This minimizes the attack surface and reduces the number of patches and updates required for maintenance.
2. Keep the ‘Admin’ account secure
The default superuser account in Windows Server is named ‘Administrator’, and most all brute force attacks are aimed at this account.
While account lockout policy can be applied to the other users, the admin user can never be locked out. The best way to keep your admin account secure is to rename the ‘Administrator’ username to something else.
3. Setup User Account Policies
If multiple users access your server, then set up User Account policies.
- Don’t allow empty passwords.
- Enforce minimum password length and complexity.
- Use lockout policy.
- Don’t store passwords using reversible encryption.
- Force session timeout for inactivity.
- Enable two-factor authentication.
- Use a password manager like LastPass or Dashlane.
4. Employ the Principle of “Least Privilege“
- Avoid potential security issues due to mishandling of access rights.
- Provide the minimum rights each user needs to carrying out his/her duties (especially on the OS partition).
- Set up Group Policy or use Role Base Access Control (RBAC) component to specify access restrictions according to your own requirements.
5. Disable unnecessary network ports and services
- Only enable the network ports used by the OS and installed components.
- Disable/close the remaining ports.
- Run a port scan of the system to confirm that all non-functional ports are properly protected.
- Disable all unused network services (Bluetooth, wifi, etc) to prevent unauthorized access.
6. Enable Windows Firewall and Antivirus
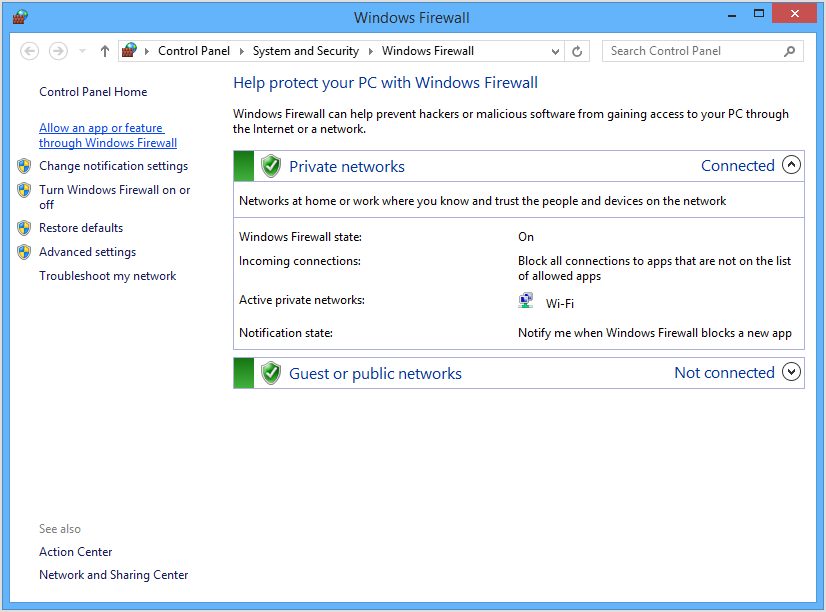
Use the Windows Firewall to filter out untrusted network traffic. Admittedly, the firewall can be difficult to master at first. But never disable the firewall! The inconveniences of setting it up properly are worth the effort.
Pro Tip: A trusted antivirus software is also recommended, to detect and eliminate security threats, viruses and other malware.
7. Use Windows BitLocker Drive Encryption

Windows BitLocker Drive Encryption secures the operating system booting process and prevent unauthorized data mining. BitLocker Drive Encryption works even when the server is not powered on! It’s a very effective anti-hacking tool against malware hacking.
8. Secure Remote Desktop (RDP)

Hackers often gain entry using RDP. To prevent unauthorized access, change the default RDP port from 3389 to one in the 10000-65535 range. If using a dedicated IP address to connect, then you can use Advanced Windows Firewall Options and lock down RDP access to that specific IP address only. Also a good way to protect your data is to use VPN. A service like cooltechzone will give you the best options for that. And, Android mobile device management allows you to configure network settings to ensure data is transmitted securely over Wi-Fi and cellular networks.
9. Use of Microsoft Baseline Security Analyzer (MBSA)
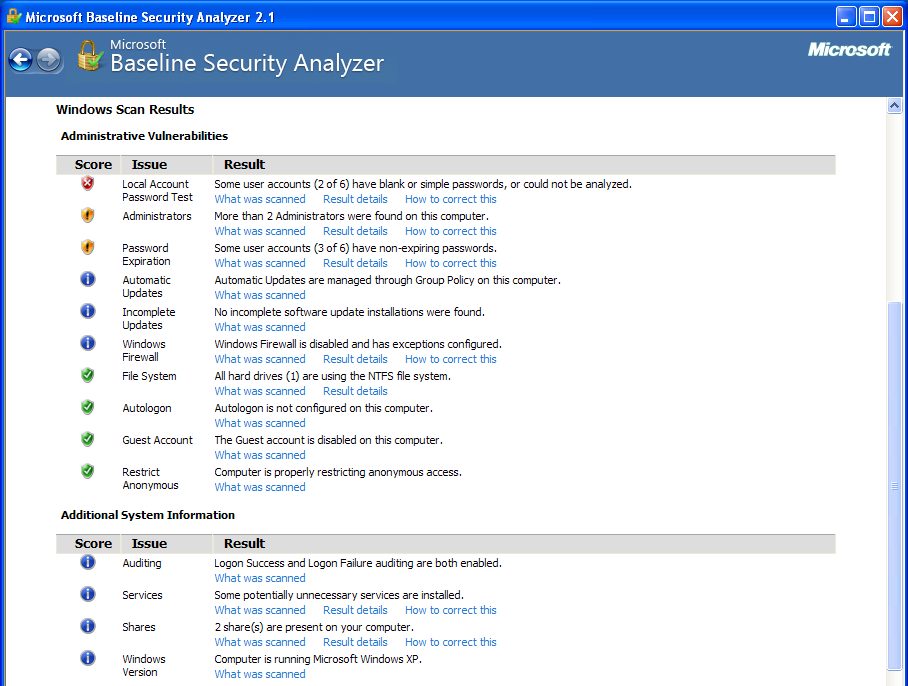
MBSA is a free application to determine missing security updates and vulnerable security settings within in Windows. It not only provides detailed insights on vulnerable components and settings, but lists possible measures to harden the server.
10. Keep Windows Updated!

And finally, as always, keep Windows update. This is one of the simplest ways to help keep your server secure. You can either configure Windows Update to notify you when a new update is available., or allow it to download and apply the update automatically.
What’s Next?
At EuroVPS, server security is not optional – it’s our mandate.
Most hosts just deploy a default Windows install, apply some MS updates/patches, and let you be on your way. But you’re not safe that way.
If Windows server security is also your concern, then give EuroVPS a try. Instead of taking your chances using an unmanaged server, try a fully managed Windows VPS. With our fully managed hosting, you can focus on your sites and content, and we’ll handle the rest.